Trusted Research Environments¶
Trusted Research Environments (TREs) are secure data analysis platforms for researchers to access and analyse sensitive data. TREs are an essential way of managing risk for unauthorised access and/or re-identification of individuals from de-identified data. The re-identification risk amplifies with increased data linkage across a wider range of disparate datasets and to date, most of the focus for TREs has been to manage information security within their environments using defined processes, people and technology.
TREs are fundamentally architected to manage the data lifecycle - data acquisition, cleaning, harmonisation, preparation, provisioning & deprovisioning and an analytics environment in support of research projects. Some TREs also provide data access management services as a delegated data access committee acting on behalf of Data Custodians. In many instances, TREs are co-located with the Data Custodians and often departments within the same organisation.
Historically, data custodians have operated on a “data release” model, where once a data access request has been granted for a research project, the required dataset is prepared (minimised and optionally linked) and released to the research project members for analysis within their own secure environment. In this model most of the risk-minimisation steps (statistical disclosure control policies) are performed upfront before releasing the data to the researchers. This adds complexity both in terms of time and effort for the data custodians to prepare the data, and often reduces the fidelity of the data for research purposes. It also additional imposes certain constraints on the receiving IT infrastructure both in terms of handling sensitive data and in terms of processing such data.
This is NOT to say this model is not appropriate nor any less secure than newer TRE based approaches, but rather TREs provide additional additional value to researchers and transparency to the public:
- In terms of handing sensitive data due to familiarity of handling similar data types
- Economies of scale due to consolidation of capability and capacity to deliver consistent processing methods
- Possibility to implement new governance approaches that allows researchers to access higher fidelity and sensitive data without minimisation and/or de-identification with proportionate security perimeter constraints on what types of analysis and data that can be exported with measures to minimise re-identifiability risk via standardised statistical disclosure control policies.
TREs, in of themselves, do not automatically engender public trust, and there are a lot of challenges that are yet to resolved, but in many scenarios can provide more holistic transparency to researchers & public, and provide mechanisms for the standard implementation of security best practices. This is harder to achieve in a traditional one-to-one “data release” model.
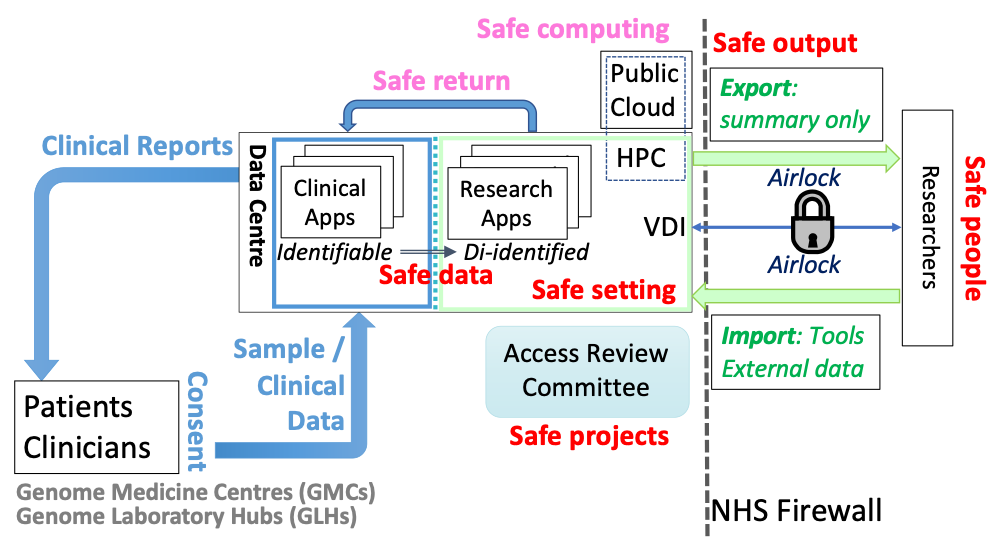
The UK Health Data Research Alliance informed by a workshop in March 2020 and subsequent stakeholder consultations during May-June 2020, published its green paper entitled "Trusted Research Environments (TRE): A strategy to build public trust and meet changing health data science needs”. It signalled a decisive pivot away from the traditional “data release” models to a model where the analysis (and analyst) accesses the data through a secure remote access service using the Five Safes framework (SAFE People accessing SAFE Data within a SAFE Settings to undertake SAFE Projects resulting in SAFE Outputs) developed by Office for National Statistics (ONS) and supported by Administrative Data Research UK (ADR UK).
Roles and Responsibilities¶
Each TRE environment will have users with multiple roles. These roles are modelled around responsibilities for each role. These roles are not mutually exclusive and one person can have multiple roles assigned. Before provisioning a Trusted Research Environment, we must consider your local setting and have an understanding of which roles are applicable to your TRE.
Role & Responsibilities Overview¶
We have outlined nine different roles and their corresponding responsibilities. Not all of them are required in all settings, but some are required for a base level TRE to function.
In many instances a TRE Administrator role is separate from the day-to-day functioning of a Data Custodian, where this may not be the case, i.e. Data Custodian and TRE Administrator are the same or a TRE Administrator has delegated authority to provide access to datasets on behalf of a Data Custodian, then both roles many apply simultaneously.
| Role ID | Role | Responsibilities | Min Req. |
|---|---|---|---|
| DC | Data Custodian | Manages data assets within a TRE environment and provides access to Researchers requesting access to data assets | ✔︎ |
| TP | TRE Provider | Provisions, administrates and maintains the multi- or single tenant TRE solution on an underlying infrastructure service | ✔︎ |
| TA | TRE Administrator | Manages the day-to-day operations of the TRE solution without access to the underlying infrastructure | |
| TD | TRE Developer | Software Developer that contributes to the development of the TRE solution | |
| DE | TRE Data Engineer | Manages the {de}provisioning of data assets within the TRE environment. This role may also have output checking responsibilities post-analysis by Researchers | ✔︎ |
| SI | TRE Service Integrator | Integrates and deploys services and modules within a project workspace. If a self-service model of operations is adopted for a TRE, this may also be a Researcher / Project/Workspace Owner or Researcher. | |
| PO | Project/Workspace Owner | Owns a specific project workspace (tenancy) within a TRE solution and has additional privileges beyond a typical researcher. They may also be a Researcher themselves | |
| RE | Project Researcher | Has access to one or more project workspaces and can use all of ther services within the project workspace | ✔︎ |
| SO | Information Security Officer | Understands the security posture of the TRE provision to ensure that the organisation is compliant with the information governance framework and relevant regulations. | ✔︎ |
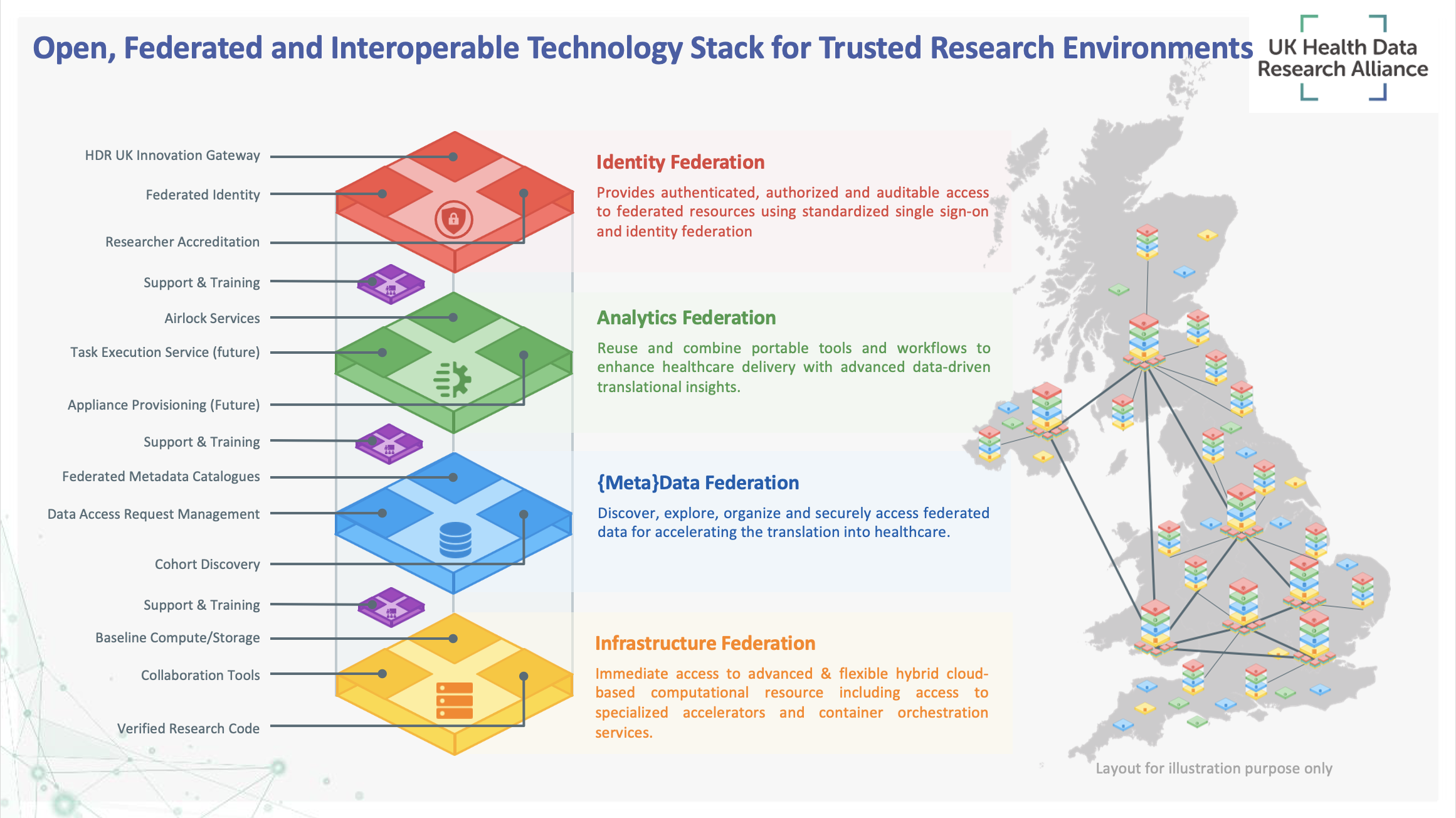
HDR UK’s focus has been leveraging existing technical capabilities where available and aligning these capabilities to be interoperable in a wider nationwide network. HDR UK does not ‘own’ or run any TREs. It has purposely focussed on capability development and interoperability between TREs rather than technology implementations and/or recommendations, as the latter are often decisions that reflect the operational context and maturity of the TRE.